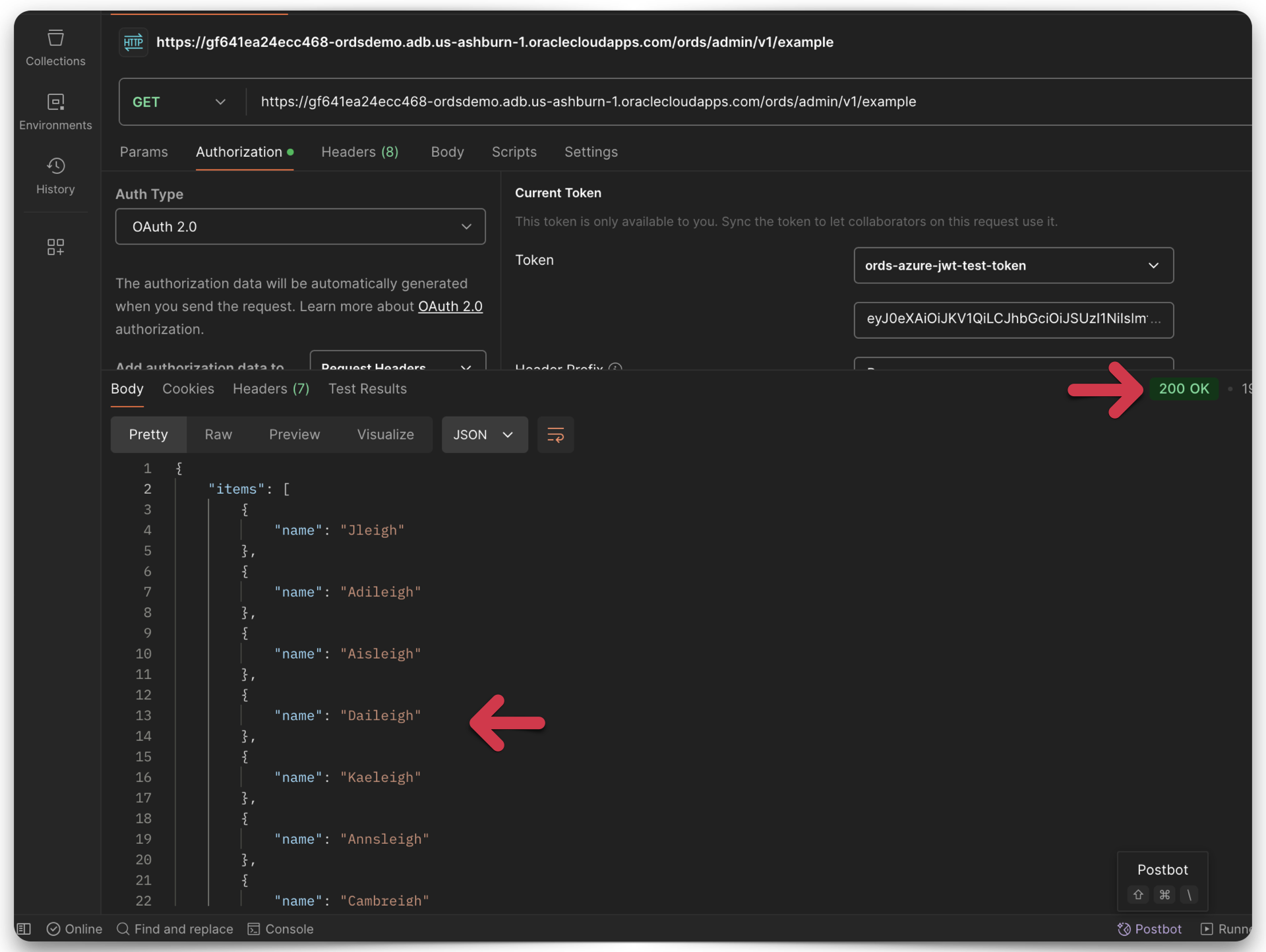
Tag: oauth 2.0
-
Configuring OCI IAM Domain JWTs to use with ORDS OAuth2.0 protected APIs
Table of Contents Intended Audience/Purpose Does this describe you? Creating a Domain Configure Client Access Adding an Integrated Application to the Domain Adding the application Configuring OAuth Resource server configuration Client Configuration Issuing a POST request to obtain a JWT Gathering the required values for the request Setting up Postman Requesting the JWT ORDS configuration…
Written by